The Boundary That
Doesn't Exist
Why most organizations operating under a Dual-Core mandate have approved a governance architecture they have never actually built.
There is a distinction that organizations executing under a Dual-Core mandate consistently fail to maintain — not in their strategy documents, not in their board resolutions, and certainly not in their execution environments.
The distinction is this: approving a governance architecture is not the same as building one.
Every organization that has adopted some version of the bifurcated operating model — a transient product and technology layer running on top of a stable, protected organizational core — has made a decision about what the institution is obligated to protect. That decision is fiduciary. It specifies that certain capabilities are institutional capital, not competitive inputs. It says, in formal terms: this is what we are governed to preserve.
What it does not say — what the vast majority of boards have never formally specified — is where the line is, what happens when it is crossed, and who owns the consequences.
That silence is not a strategic gap. It is a structural governance failure. And it is most acute not in organizations that have ignored governance entirely — but in organizations that believe they have already addressed it. The board that has chartered an AI oversight committee, published an agility mandate, and designated a "core" is the board most likely to be operating without the three structural elements that make any of those instruments enforceable. The architecture looks complete from the boardroom. The boundary still doesn't exist.
The Myth That Passes for Governance
The prevailing assumption is that a board mandate to bifurcate the operating model constitutes a governance decision. It does not. A mandate is a statement of intent. Governance is the architecture that enforces that intent against the friction of execution, against the incentives of autonomous systems and decentralized teams, against the compression of technology cycles that eliminates the temporal checkpoints that previously provided implicit, if inadequate, oversight.
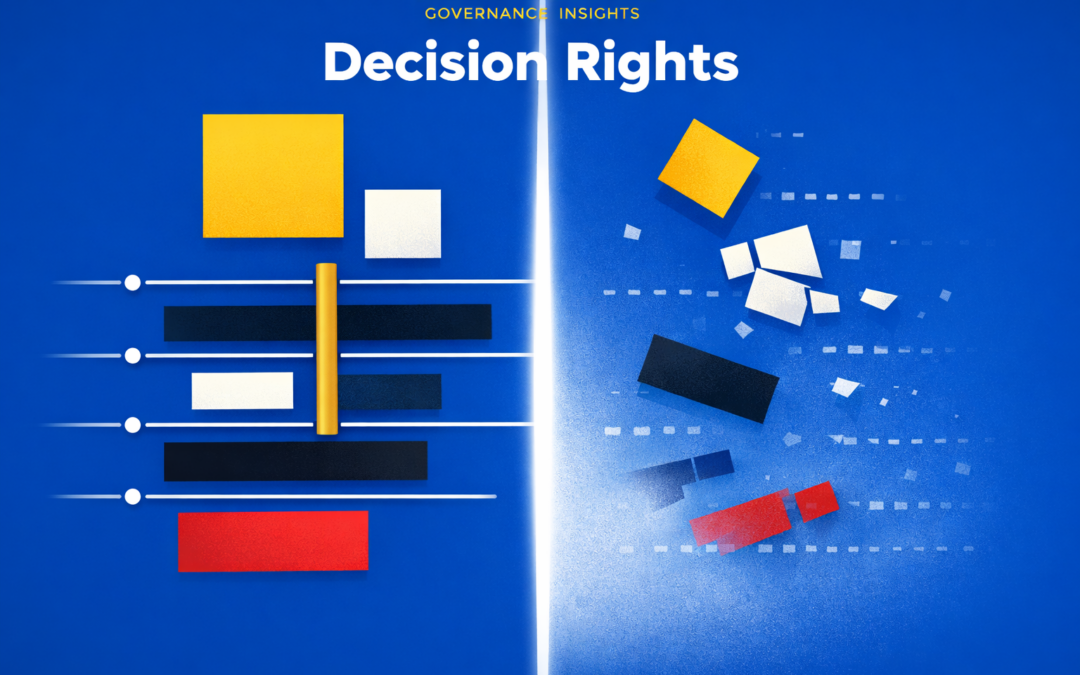
The governance failure is not that boards are approving the wrong strategy. The failure is that they are treating strategy approval as a substitute for the three structural elements that make a strategy governable:
Without all three, sequentially and formally, what organizations have is not a Dual-Core mandate. They have a Dual-Core aspiration operating in a single-layer governance environment. The transient execution layer has authority. The sustainable core has a name. But the line between them has never been drawn, the signals that indicate it is being crossed have never been specified, and no one owns the consequences when it is.
This is not a theoretical vulnerability. It is the structure through which organizational core degradation propagates undetected — typically long after the damage has become irreversible.
What the Three-Component Architecture Actually Requires
The decision-rights boundary is not a policy statement. It is a structural specification with three required components, each of which is a precondition for the next, and none of which can be substituted by cultural intent or executive judgment. The sequence is causally enforced: the threshold specification has nothing to operationalize without a defined scope; the accountability chain has nothing to activate without thresholds that trigger it. Removing any component does not produce a partial boundary. It produces no boundary at all.
The foundational instrument is a formal categorical inventory: which organizational capabilities are designated as core stability assets, subject to protection from transformation velocity, and which are designated as transient execution assets, subject to active rotation. Core stability assets are not abstract — they include the talent capability pools the institution depends on for execution quality, the proprietary data infrastructure that underpins competitive differentiation, the institutional trust relationships that cannot be rebuilt quickly, and the organizational health systems that sustain performance across cycles. These are the capabilities that, once degraded by unconstrained transformation velocity, cannot be restored by the next strategic initiative.
The word formal carries precise weight here. The inventory must be approved at board level, not delegated to the executive committee. This is not a procedural preference. It is the governance mechanism that creates fiduciary accountability.
An executive-committee-approved boundary protects the executive committee from operational friction. It can be revised, reinterpreted, or quietly set aside when transformation velocity creates pressure to do so. A board-approved boundary creates a different category of obligation. It specifies what the board has determined the institution is chartered to protect. Its revision requires board-level deliberation. Its violation is not an execution problem. It is a governance problem — with corresponding accountability implications.
Most organizations operating under an agility mandate today have this inventory nowhere. The "core" is a rhetorical category, not a formal one. The capabilities it is supposed to protect are understood culturally, not specified institutionally. When transformation initiatives approach those capabilities, there is no instrument governing the boundary. There is only judgment — which is to say, there is no governance instrument at all.
Even a formally approved scope definition is insufficient without the second component: a set of quantitative thresholds that define precisely when autonomous execution authority is suspended and mandatory governance escalation is required.
Thresholds must be defined by capability domain, by decision type, and by risk tier. Their purpose is to operationalize the scope definition — to translate the categorical protection of core stability assets into actionable governance signals. When an R&D reallocation initiative approaches the bandwidth beyond which organizational core degradation becomes measurable, the threshold triggers escalation before the boundary is crossed, not after it has been breached at scale.
The empirical evidence on what those thresholds approximate at the organizational level exists. McKinsey's innovation benchmarks document that top-quartile innovators operate within a reallocation bandwidth of 6% to 30% of annual R&D budgets before core stability is jeopardized. (This is not a governance threshold specification in itself — domain-specific and risk-tier calibration is required — but it establishes the governing principle: empirical thresholds exist, are measurable, and carry material organizational consequences when crossed without formal governance activation.)
The absence of threshold specifications means every transformation initiative operating against core stability assets is governed by implicit defaults. Implicit defaults are not fiduciarily defensible. They are the structural equivalent of deploying an AI system without defining the decision authority that governs its execution — which, for organizations accelerating both their transformation layer and their autonomous AI deployment simultaneously, is no longer a hypothetical parallel. It is the operating environment.
The third component is the most frequently omitted and the most consequential: a formally chartered accountability structure that owns outcomes when thresholds are crossed.
The specification requirements are precise: which committee receives escalation, what the documented response protocol requires, and — critically — how the board is notified independent of management reporting.
That last specification is not procedural. It is architectural. Information pipelines designed for human decision chains run through the same management layer that has organizational incentives to filter, delay, or reframe degradation signals before they reach the board. An accountability chain that depends on management to activate it is not an independent oversight instrument. It is a reporting mechanism dressed in the language of governance.
The consequence is concrete and documented. The Deloitte AI Risk Governance Survey (2025) records a 12-to-18-month lag between AI governance failures and board-level visibility — a gap produced precisely by accountability chains that route through management rather than bypassing it. The structural parallel to transformation governance is exact: when the accountability chain is designed to pass through the layer it was designed to oversee, degradation accumulates invisibly until it is no longer correctable at the board level. Independent notification architecture — a direct pipeline from threshold-crossing detection to board visibility, bypassing management interpretation — is not a governance enhancement. It is what separates a governance instrument from an organisational reporting structure.
Machine Speed, Human-Speed Governance
The three-component architecture described above was structurally necessary before AI acceleration became a factor. Its absence was already producing the governance failures this framework addresses. What AI deployment does is eliminate the temporal friction that previously provided implicit constraint.
Human-speed execution creates natural checkpoints. Decisions accumulate into visible patterns. Degradation signals emerge at a pace that, even without formal governance instruments, occasionally surfaces through standard reporting channels before consequences become irreversible. Machine-speed execution eliminates that friction entirely. Autonomous systems operating against a core-transient architecture without a formally defined boundary do not slow down at the line. They accelerate through it.
Organizations that have deployed AI augmentation across their transformation architecture without first establishing the three-component boundary are not executing the Dual-Core mandate at greater velocity. They are executing the Dual-Core aspiration — the version where the core is named but not governed — at the velocity of an autonomous system. The governance gap that existed at human speed now operates at machine speed with no degradation friction and no natural checkpoint.
The formal boundary is not a constraint on AI acceleration. It is the precondition for AI acceleration that doesn't consume the organizational core it is designed to operate against.
The Structural Reframe
The prevailing myth this piece challenges is the one embedded in the language of agile governance itself: that formal boundary definition introduces rigidity into environments requiring continuous reconfiguration, and that the cost of maintaining formal decision-rights boundaries exceeds the liability exposure such boundaries prevent.
The argument misidentifies what a boundary governs. Formal boundary instruments are not constraints on transient execution. They are constraints on transient execution's authority to consume the core. The boundary does not reduce the malleability of the product layer. It defines the perimeter within which that malleability operates.
An organization that can reconfigure its product portfolio at competitive velocity, within a formally governed core stability boundary, is not less agile than one operating without that boundary. It is executing agility against a protected asset base — rather than executing agility against an asset base it is simultaneously degrading. Amazon's governance of the AWS separation is the empirical proof: a formally protected infrastructure core, insulated from the rotation velocity governing the retail and marketplace layer, did not constrain Amazon's transient expansion into streaming, healthcare, logistics, and advertising. It enabled it.
The distinction is not semantic. It is the difference between transformation as competitive strategy and transformation as structural self-consumption at scale.
The Sequence That Cannot Be Compressed
One implication of the three-component architecture deserves explicit statement: the components are sequential. The threshold specification has no function without the scope definition it operationalizes. The accountability chain has nothing to activate without the thresholds that trigger it. Boards that have chartered AI oversight committees, established escalation protocols, and deployed governance dashboards — but have not formally approved the scope definition that specifies what the organization is chartered to protect — have built their governance architecture on an unspecified foundation.
The sequence cannot be compressed. The scope definition is not one governance priority among several. It is the load-bearing structural element from which every subsequent governance instrument extends. Boards that have not formally established it will encounter its absence as a compounding liability at every subsequent layer.
The gap does not remain contained to the layer where it originates.
It propagates.